- cross-posted to:
- technology@lemmy.world
- cross-posted to:
- technology@lemmy.world
This affects Signal too
An issue with Cloudflare allows an attacker to find which Cloudflare data center a messaging app used to cache an image, meaning an attacker can obtain the approximate location of Signal, Discord, Twitter/X, and likely other chat app users. In some cases an attacker only needs to send an image across the app, with the target not clicking it, to obtain their location.
https://gist.github.com/hackermondev/45a3cdfa52246f1d1201c1e8cdef6117?ref=404media.co
Signal, an open-source encrypted messaging service, is widely used by journalists and activists for its privacy features. Internally, the app utilizes two CDNs for serving content: cdn.signal.org (powered by CloudFront) for profile avatars and cdn2.signal.org (powered by Cloudflare) for message attachments.


Fun fact, you can always use timing attacks to narrow down a location.
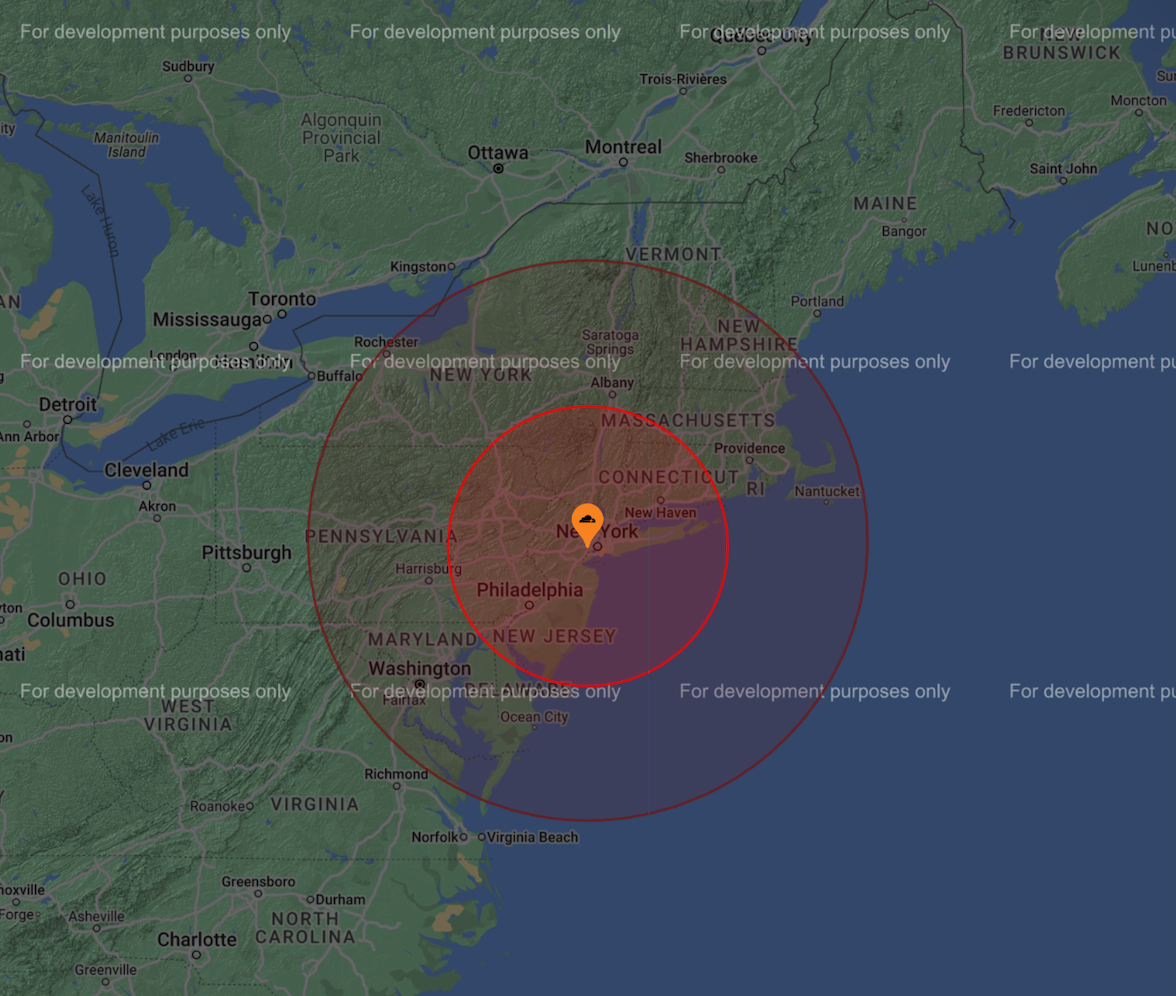
The target sends some traffic to multiple geographic sites. Looking at the response timing of that traffic gives you a maximum radius from each site. Overlay multiple radiuses and you get a workable approximate
Great point. The range shown in the article doesn’t seem to be that big of a deal for me, but I suppose it could matter for some situations.